Password Cracking and Reverse Engineering Tutorial
Introduction
As students of network security, we have seen time and time again how weak passwords often pave the easiest path to a user's machine; as the common saying goes, there is no patch for human stupidity. That being said, this tutorial will demonstrate how the cracking of a simple password can expose a user to a multitude of web attacks. We have set up a simple website that asks the user for login credentials, in order to access a secure page on the web server. By capturing this login traffic, the attacker can perform an offline brute-force password crack to recover the password and login of that user. This is valuable because it gives the attacker full access to that user's information stored on the website (e.g. a bank account).
Overview of tutorial
- Sniff the login traffic with tcpdump
- Analyze the traffic with Wireshark
- Crack the password with JtR
Remote Packet Sniffing (use our password2.pcap)
We recognize that once you have a shell on the remote machine there are a lot of things that you can do; however, you may not be looking to compromise a machine, but rather learn about a user's habits. In this case, you will be capturing packets of a user as he or she logs into a website. To accomplish this, we will be using tcpdump to sniff network traffic, and Wireshark to extract relevant packet data. It's worth noting that Wireshark is very capable of capturing packets locally; however, the high amount of overhead needed to run its full GUI over SSH makes tcpdump a better solution for remote capturing. To run tcpdump, use a command of the following format:
sudo tcpdump -i INTERFACE -s 0 -w FILE
Note that tcpdump requires elevated privileges to read packets directly from a network interface. Since we can't give you sudo access to the class machines, you can download a sufficient packet capture from here, password.pcap.
The -s 0 flag means not to truncate the packets that tcpdump captures. In fact, there are tons of tcpdump options, including options for real-time monitoring, filtering by port/interface/flags/protocol/host, as well as several formatting options for the output.
Analysis of packet file
Once you have retrieved the tcp packet dump, you will need to examine its contents using Wireshark. Being that Wireshark runs with a GUI, we will need to setup X11 forwarding, which will allow us to forward the windows from an SSH connection to our local machine. To do this, logout of any SSH session you have running, and reconnect to hamsa with the -X flag. Since the GUI over SSH produces a lot of traffic, consider doing this part with a partner or else on your local machine:
$ ssh -X USER@hamsa.cs.northwestern.edu
After logging in, run Wireshark. Open the capture file from wherever it was saved in the previous step and you will see something similiar to what is shown below:
$ wireshark packetdumpname.pcap
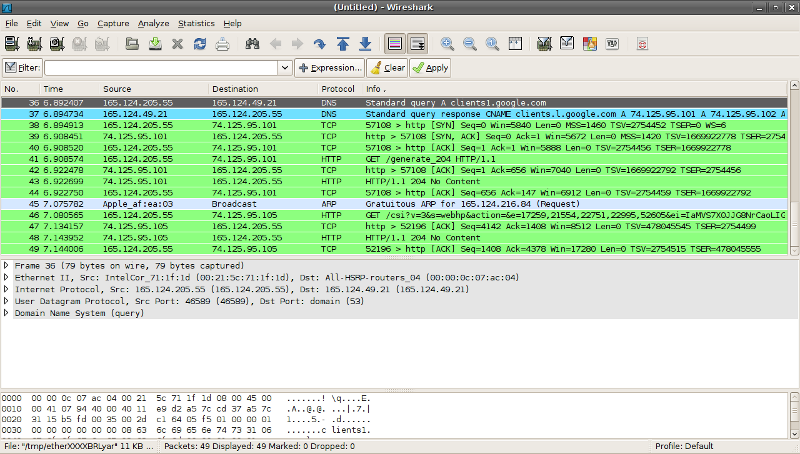
Wireshark's filter textbox can be used to limit the packets shown to those of interest. Since we know that we are only concerned with HTTP traffic, this might be a good place to start. Wireshark is a powerful tool on which an entire tutorial could be written, but the Wireshark Wiki is a great place to start. To give you some hints for this portion of the exploit, the user will browse some websites before attempting to login to the server in question. Your goal is to through the packets and find the one where he sends his credentials and logs into a site. Another hint, his credentials are sent in the clear, but not in plain text. Try looking for something that is base64 encoded. You'll have to reverse the base64, but that's not too difficult. Here's some Ruby code that uses base64 encoded and decoded strings:
require 'base64'
str = 'mybase64encodedstring'
decoded = Base64.decode64(str)
puts decoded
encoded = Base64.b64encode(str)
puts encoded
Once you have found the username and password, you can replay his password to the secure server. A replay is an attack where sniffed data is resent to a server, and the server accepts it as valid. Often, systems that do poor session handling and do not encrypt traffic are vulnerable to replay attacks. A note, his password will look strong, but don't let that scare you.
Use John the Ripper to recover the plaintext of the password. Unfortunately, John the Ripper's MD5-cracking scheme only supports the FreeBSD implementation of MD5 (which is not standard MD5 as we know it). To get around this, we are supplying a patched version of John the Ripper that supports raw MD5 cracking (found here). After extracting the directory, create a text file containing the hashed password recovered in the previous step: user:HASHEDPASSWORD. This format is required by John the Ripper. Putting it all together...
$ tar -xf newjohn2.tar
$ cd john
$ ./john PASSWORDFILE.txt
Loaded 1 password (FreeBSD MD5 [32/32])
nottheactualpassword (user)
guesses: 1 time: 0:82:20:09 c/s: 4816K trying: ...
It's worth noting that for passwords not in a dictionary list, the --incremental flag tells John the Ripper to simply try every permutation possible (read: do not try this for long passwords).
Report to the instructor about the acquired password and user name.
Online brute force attack (Not required for class exercise)
To begin our tutorial, we will use an online password cracking program called Hydra. Running off of a word list, Hydra speeds up the process of cracking weak password by running multiple instances of the attack against a specified service (e.g. SSH, which defaults to 16 simultaneous threads). Word lists form the backbone of this attack and can be found all over the internet. For our purposes, we will use a short wordlist from the Openwall wordlists collection. The machine you will try to exploit is running an SSH server and includes a user with a weak password.
You must execute an SSH brute force attack on the machine with hydra, a network login cracker.
A basic Hydra command may look like the following, which attempts to guess the SSH password of user on netsec-playground:
hydra -l user -P lower -t 1 netsec-playground ssh2
Scaning over the password dictionary will take a few hours, so it is not required in the class exercise.
Common command line flags
-
-lSpecifies one or more usernames (space separated). -
-LSpecifies a file of usernames. -
-pSpecifies one or more passwords (space separated). -
-PSpecifies a file of passwords. -
-tSpecifies the number of threads to spawn to run the crack. Note that some services will automatically limit this (e.g. VNC). -
-sSpecifies the port on which to access the service, if different from the default. -
-fQuits after finding a single correct login/password pair. -
-vExecute in verbose mode.
Upon a successful run, Hydra output may look like the following:
Hydra v5.4 (c) 2006 by van Hauser / THC - use allowed only for legal purposes.
Hydra (http://www.thc.org) starting at 2002-2-01 15:58:50
[DATA] 16 tasks, 1 servers, 27414 login tries (l:1/p:27414), ~1713 tries per task
[DATA] attacking service ssh2 on port 22
[22][ssh2] host: 192.168.1.5 login: user password: pass
[STATUS] attack finished for remote-machine (waiting for childs to finish)
Hydra (http://www.thc.org) finished at 2002-2-01 15:59:30
Using Hydra, attempt to crack the weak user's password on the machine, and then login with SSH. Limit the number of threads spawned by Hydra to 4 or 8 to avoid taking down the machine everyone's trying to exploit.
Copyright 2009 the following: Patrick Foley patrickfoley2011@u.northwestern.edu Jun Hu jun-hu@northwestern.edu Brett Parker brettpark2011@u.northwestern.edu Dmitry Spivak dima@northwestern.edu All rights reserved. Permission to reproduce this document in whole or in part must be obtained from the authors. Edited by Shamiq Islam i.shamiq@gmail.com